How to Set Up WireGuard VPN on CentOS 8
Published on
•8 min read

WireGuard is a simple and modern VPN (Virtual Private Network) with state-of-the-art cryptography. It is faster, easier to configure, and more performant than other similar solutions, such as IPsec and OpenVPN .
WireGuard is cross-platform and can run almost anywhere, including Linux, Windows, Android, and macOS. Wireguard is a peer-to-peer VPN; it not based on the client-server model. Depending on its configuration, a peer can act as a traditional server or client.
WireGuard works by creating a network interface on each peer device that operates as a tunnel. Peers authenticate each other by exchanging and validating public keys, mimicking the SSH model. Public keys are mapped with a list of IP addresses that are allowed in the tunnel. The VPN traffic is encapsulated in UDP.
This tutorial describes how to set up WireGuard on a CentOS 8 machine that will act as a VPN server. We’ll also show you how to configure WireGuard as a client. The client’s traffic will be routed through the CentOS 8 server. This setup can be used as a protection against Man in the Middle attacks, surfing the web anonymously, bypassing Geo-restricted content, or allowing your colleagues who work from home to connect to the company network securely.
Prerequisites
You’ll need a CentOS 8 server that you can access as root or account with sudo privileges .
Setting Up the WireGuard Server
We’ll start by installing WireGuard on the CentOS machine and set it up to act as a server. We’ll also configure the system to route the clients’ traffic through it.
Installing WireGuard on CentOS 8
WireGuard tools and kernel module are available for installation from the Epel and Elrepo repositories. To add the repositories to your system, run the following command:
sudo dnf install epel-release elrepo-release Once done, install the WireGuard packages:
sudo dnf install kmod-wireguard wireguard-toolsYou may be asked to import the repositories GPG Keys. Type y when prompted.
Configuring WireGuard
The wireguard-tools package includes two command-line tools named wg and wg-quick that allow you to configure and manage the WireGuard interfaces.
We’ll store the VPN server configuration and in the /etc/wireguard directory. On CentOS, this directory is not created during the installation. Run the following command to create the directory
:
sudo mkdir /etc/wireguardGenerate the public and private keys in the /etc/wireguard directory.
wg genkey | sudo tee /etc/wireguard/privatekey | wg pubkey | sudo tee /etc/wireguard/publickeyYou can view the files with cat
or less
. The private key should never be shared with anyone.
Now that the keys are generated, the next step is to configure the tunnel device that will route the VPN traffic.
The device can be set up either from the command line using the ip
and wg or by creating the configuration file with a text editor.
Create a new file named wg0.conf and add the following contents:
sudo nano /etc/wireguard/wg0.conf[Interface]
Address = 10.0.0.1/24
SaveConfig = true
ListenPort = 51820
PrivateKey = SERVER_PRIVATE_KEY
PostUp = firewall-cmd --zone=public --add-port 51820/udp && firewall-cmd --zone=public --add-masquerade
PostDown = firewall-cmd --zone=public --remove-port 51820/udp && firewall-cmd --zone=public --remove-masquerade
The interface can be named anything you want, however it is recommended to use something like wg0 or wgvpn0. The settings in the interface section have the following meaning:
Address - a comma-separated list of v4 or v6 IP addresses for the
wg0interface. Use IPs from a range that is reserved for the private networks (10.0.0.0/8, 172.16.0.0/12 or 192.168.0.0/16).ListenPort - the port on which WireGuard will accept incoming connections.
PrivateKey - a private key generated by the
wg genkeycommand. (To see the contents of the file run:sudo cat /etc/wireguard/privatekey)SaveConfig - when set to true, the current state of the interface is saved to the configuration file when shutdown.
PostUp - command or script which is executed before bringing the interface up. In this example, we’re using
firewall-cmdto open the WireGuard port and enable masquerading. This will allow traffic to leave the server, giving the VPN clients access to the Internet.PostDown - command or script which is executed before bringing the interface down. The firewall rules will be removed once the interface is down.
The wg0.conf and privatekey files should not be readable to normal users. Use chmod
to set the permissions to 600:
sudo chmod 600 /etc/wireguard/{privatekey,wg0.conf}Once done, bring the wg0 interface up using the attributes specified in the configuration file:
sudo wg-quick up wg0The command will output something like this:
[#] ip link add wg0 type wireguard
[#] wg setconf wg0 /dev/fd/63
[#] ip -4 address add 10.0.0.1/24 dev wg0
[#] ip link set mtu 1420 up dev wg0
[#] iptables -A FORWARD -i wg0 -j ACCEPT; iptables -t nat -A POSTROUTING -o ens3 -j MASQUERADE
To view the interface state and configuration, run:
sudo wg show wg0interface: wg0
public key: My3uqg8LL9S3XZBo8alclOjiNkp+T6GfxS+Xhn5a40I=
private key: (hidden)
listening port: 51820
You can also use the ip command to verify the interface state:
ip a show wg04: wg0: <POINTOPOINT,NOARP,UP,LOWER_UP> mtu 1420 qdisc noqueue state UNKNOWN group default qlen 1000
link/none
inet 10.0.0.1/24 scope global wg0
valid_lft forever preferred_lft forever
To bring the wg0 interface at boot time run the following command:
sudo systemctl enable wg-quick@wg0Server Networking
For NAT to work, we need to enable IP forwarding. Create a new file /etc/sysctl.d/99-custom.conf, and add the following line:
sudo nano /etc/sysctl.d/99-custom.confnet.ipv4.ip_forward=1Save the file and apply the change using sysctl
:
sudo sysctl -p /etc/sysctl.d/99-custom.confnet.ipv4.ip_forward = 1
That’s it. The CentOS peer that will act as a server has been set up.
Linux and macOS Clients Setup
The installation instructions for all supported platforms are available at https://wireguard.com/install/
. On Linux systems, you can install the package using the distribution package manager and on macOS with brew. Once you install WireGuard, follow the steps below to configure the client device.
The process for setting up a Linux and macOS client is pretty much the same as you did for the server. Start by generating the public and private keys:
wg genkey | sudo tee /etc/wireguard/privatekey | wg pubkey | sudo tee /etc/wireguard/publickeyCreate the file wg0.conf and add the following contents:
sudo nano /etc/wireguard/wg0.conf[Interface]
PrivateKey = CLIENT_PRIVATE_KEY
Address = 10.0.0.2/24
[Peer]
PublicKey = SERVER_PUBLIC_KEY
Endpoint = SERVER_IP_ADDRESS:51820
AllowedIPs = 0.0.0.0/0
The settings in the interface section have the same meaning as when setting up the server:
- Address - a comma-separated list of v4 or v6 IP addresses for the
wg0interface. - PrivateKey - To see the contents of the file on the client machine run:
sudo cat /etc/wireguard/privatekey
The peer section contains the following fields:
- PublicKey - a public key of the peer you want to connect to. (The contents of the server’s
/etc/wireguard/publickeyfile). - Endpoint - an IP or hostname of the peer you want to connect to followed by a colon, and then a port number on which the remote peer listens to.
- AllowedIPs - a comma-separated list of v4 or v6 IP addresses from which incoming traffic for the peer is allowed and to which outgoing traffic for this peer is directed. We’re using 0.0.0.0/0 because we are routing the traffic and want the server peer to send packets with any source IP.
If you need to configure additional clients, just repeat the same steps using a different private IP address.
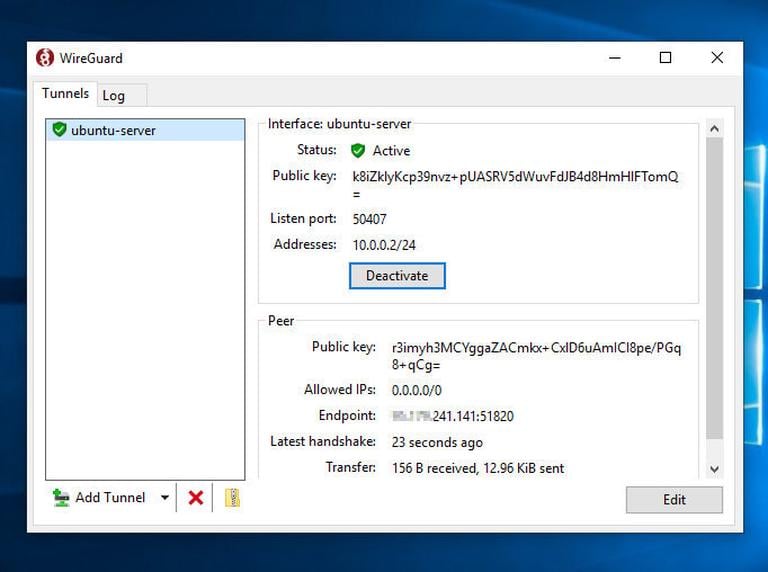
Windows Clients Setup
Download and install the Windows msi package from the WireGuard website .
Once installed open the WireGuard application and click on “Add Tunnel” -> “Add empty tunnel…” as shown on the image below:
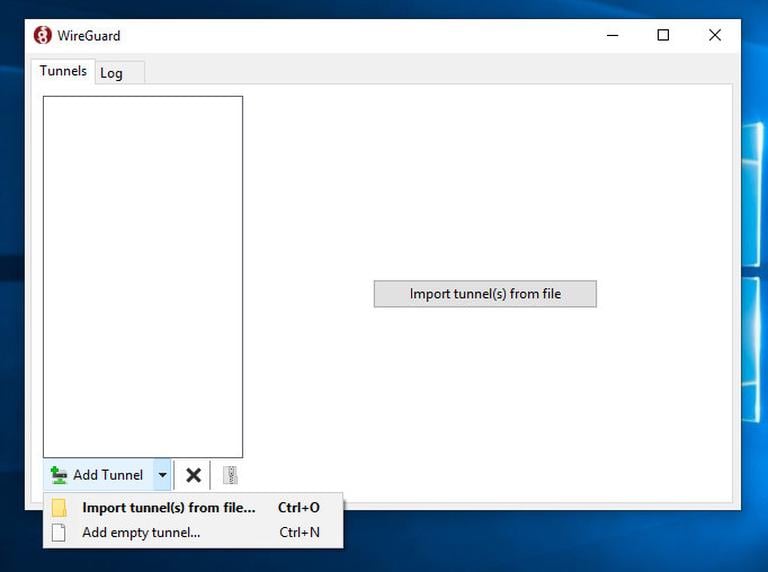
A publickey pair is automatically created and displayed on the screen.
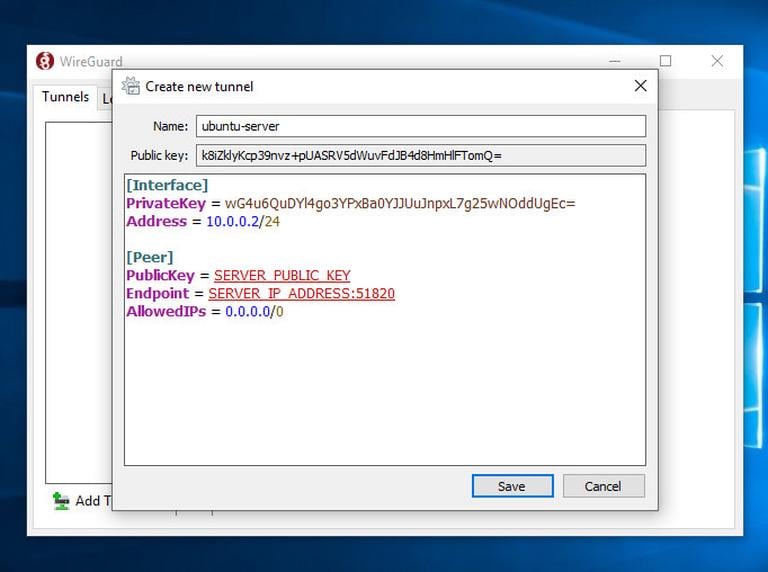
Enter a name for the tunnel and edit the configuration as follows:
[Interface]
PrivateKey = CLIENT_PRIVATE_KEY
Address = 10.0.0.2/24
[Peer]
PublicKey = SERVER_PUBLIC_KEY
Endpoint = SERVER_IP_ADDRESS:51820
AllowedIPs = 0.0.0.0/0
In the interface section add a new line to define the client tunnel Address.
In the peer section add the following fields:
- PublicKey - the public key of the CentOS server (
/etc/wireguard/publickeyfile). - Endpoint - the IP address of the CentOS server followed by a colon, and WireGuard port (51820).
- AllowedIPs - 0.0.0.0/0
Once done, click on the “Save” button.
Add the Client Peer to the Server
The last step is to add the client public key and IP address to the server:
sudo wg set wg0 peer CLIENT_PUBLIC_KEY allowed-ips 10.0.0.2Make sure to change the CLIENT_PUBLIC_KEY with the public key you generated on the client machine (sudo cat /etc/wireguard/publickey) and adjust the client IP address if it is different. Windows users can copy the public key from the WireGuard application.
Once done, go back to the client machine and bring up the tunneling interface.
Linux and macOS Clients
On Linux clients run the following command the bring up the interface:
sudo wg-quick up wg0Now you should be connected to the CentOS server, and the traffic from your client machine should be routed through it. You can check the connection with:
sudo wginterface: wg0
public key: sZThYo/0oECwzUsIKTa6LYXLhk+Jb/nqK4kCCP2pyFg=
private key: (hidden)
listening port: 60351
fwmark: 0xca6c
peer: My3uqg8LL9S3XZBo8alclOjiNkp+T6GfxS+Xhn5a40I=
endpoint: XXX.XXX.XXX.XXX:51820
allowed ips: 0.0.0.0/0
latest handshake: 41 seconds ago
transfer: 213.25 KiB received, 106.68 KiB sent
You can also open your browser, type “what is my ip”, and you should see your CentOS server IP address.
To stop the tunneling, bring down the wg0 interface:
sudo wg-quick down wg0Windows Clients
If you installed WireGuard on Windows, click on the “Activate” button. Once the peers are connected, the tunnel status will change to Active:
Conclusion
We have shown you how to install WireGuard on a CentOS 8 machine and configure it as a VPN server. This setup allows you to surf the web anonymously by keeping your traffic data private.
If you are facing any problems, feel free to leave a comment.