How to Set Up SSH Keys on Ubuntu 20.04
Secure Shell (SSH) is a network protocol for creating a secure connection between a client and a server. With SSH, you can run commands on remote machines, create tunnels, forward ports, and more.
SSH supports various authentication mechanisms. The two most common ones are password and public-key based authentication.
Authentication using a public key is based on the use of digital signatures, and it is more secure and convenient than traditional password authentication.
This article explains how to generate SSH keys on Ubuntu 20.04 systems. We’ll also show you how to set up an SSH key-based authentication and connect to remote Linux servers without entering a password.
Creating SSH keys on Ubuntu
The chances are that you already have an SSH key pair on your Ubuntu client machine. If you generate a new key pair, the old one will be overwritten. To check whether the key files exist, run the following ls
command:
ls -l ~/.ssh/id_*.pubIf the command returns something like No such file or directory, or no matches found, it means that the user does not have SSH keys, and you can proceed with the next step and generate SSH key pair. Otherwise, if you have an SSH key pair, you can either the existing ones or backup up the old keys and generate a new pair.
To generate a new 4096 bits SSH key pair with your email address as a comment, run:
ssh-keygen -t rsa -b 4096 -C "your_email@domain.com"You will be prompted to specify the file name:
Enter file in which to save the key (/home/yourusername/.ssh/id_rsa):The default location and file name should be fine for most users. Press Enter to accept and continue.
Next, you’ll be asked to type a secure passphrase. A passphrase adds an extra layer of security. If you set a passphrase, you’ll be prompted to enter it each time you use the key to login to the remote machine.
If you don’t want to set a passphrase, press Enter.
Enter passphrase (empty for no passphrase):The whole interaction looks like this:
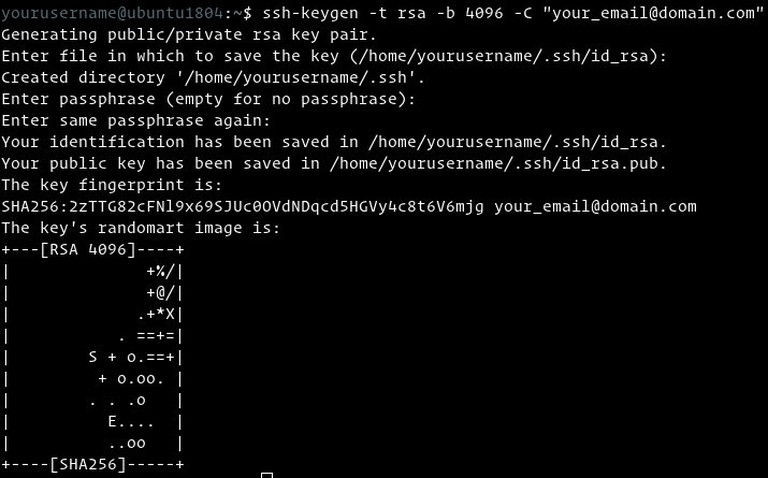
To verify your new SSH key pair is generated, type:
ls ~/.ssh/id_*/home/yourusername/.ssh/id_rsa /home/yourusername/.ssh/id_rsa.pubThat’s it. You’ve successfully generated an SSH key pair on your Ubuntu client machine.
Copy the Public Key to the Remote Server
Now that you have an SSH key pair, the next step is to copy the public key to the remote server you want to manage.
The easiest and the recommended way to copy the public key to the server is to use the ssh-copy-id tool. On your local machine type:
ssh-copy-id remote_username@server_ip_addressYou will be prompted to enter the remote user password:
remote_username@server_ip_address's password:Once the user is authenticated, the public key ~/.ssh/id_rsa.pub will be appended to the remote user ~/.ssh/authorized_keys file, and the connection will be closed.
Number of key(s) added: 1
Now try logging into the machine, with: "ssh 'username@server_ip_address'"
and check to make sure that only the key(s) you wanted were added.If by some reason the ssh-copy-id utility is not available on your local computer, use the following command to copy the public key:
cat ~/.ssh/id_rsa.pub | ssh remote_username@server_ip_address "mkdir -p ~/.ssh && chmod 700 ~/.ssh && cat >> ~/.ssh/authorized_keys && chmod 600 ~/.ssh/authorized_keys"Login to your server using SSH keys
After completing the steps above, you should be able to log in to the remote server without being prompted for a password.
To test it, try to login to your server via SSH:
ssh remote_username@server_ip_addressIf you haven’t set a passphrase for the private key, you will be logged in immediately. Otherwise, you will be prompted to enter the passphrase.
Disabling SSH Password Authentication
Disabling the password authentication adds an extra layer of security to your server.
Before disabling SSH password authentication, make sure you can log in to your server without a password, and the user you are logging in with has sudo privileges .
Log into your remote server:
ssh sudo_user@server_ip_addressOpen the SSH configuration file with your text editor :
sudo nano /etc/ssh/sshd_configSearch for the following directives and modify as it follows:
PasswordAuthentication no
ChallengeResponseAuthentication no
UsePAM noOnce done, save the file and restart the SSH service by typing:
sudo systemctl restart sshAt this point, the password-based authentication is disabled.
Conclusion
We’ve shown you how to generate a new SSH key pair and set up an SSH key-based authentication. You can use the same key to manage multiple remote servers. You have also learned how to disable SSH password authentication and add an extra layer of security to your server.
By default, SSH listens on port 22. Changing the default SSH port reduces the risk of automated attacks. To simplify your workflow, use the SSH config file to define all your SSH connections.
If you have any questions or feedback, feel free to leave a comment.
Linuxize Weekly Newsletter
A quick weekly roundup of new tutorials, news, and tips.
About the authors

Dejan Panovski
Dejan Panovski is the founder of Linuxize, an RHCSA-certified Linux system administrator and DevOps engineer based in Skopje, Macedonia. Author of 800+ Linux tutorials with 20+ years of experience turning complex Linux tasks into clear, reliable guides.
View author page